Complete History of the DNS System
From the HOSTS file to DNS over HTTPS: the evolution of the system that connects the Internet
The Domain Name System (DNS) is one of the most important and least recognized inventions of the digital age. What started as a simple text file in the 1970s has become a critical global infrastructure processing trillions of queries daily. This timeline covers the most important milestones of its evolution, from ARPANET to modern encrypted protocols.
ARPANET is Born
1969The U.S. Department of Defense creates ARPANET, the precursor network to the Internet. On October 29, the first message is sent between UCLA and the Stanford Research Institute (SRI). At this point, each connected machine is identified only by its numeric address.
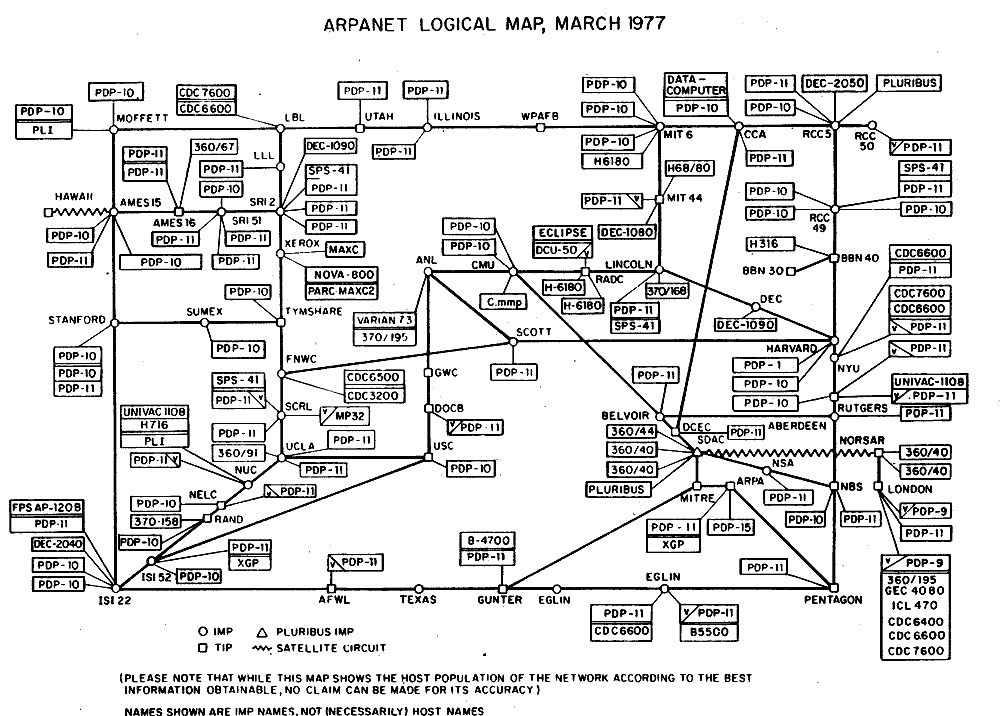
ARPANET / Dominio público
The HOSTS.TXT File
1971Elizabeth "Jake" Feinler and her team at SRI's Network Information Center (NIC) begin maintaining a centralized file called HOSTS.TXT that maps hostnames to numeric addresses. Every time a new computer was added to ARPANET, the file had to be manually updated and distributed to all network nodes.
Birth of DNS
1983With ARPANET growing rapidly, the HOSTS.TXT file becomes unmanageable. Paul Mockapetris from USC's Information Sciences Institute designs the Domain Name System (DNS) and describes it in RFC 882 and RFC 883. Jon Postel simultaneously publishes RFC 881 defining the domain structure. This moment marks the birth of the system that today resolves billions of queries daily.

Wikimedia Commons / CC BY-SA 3.0
First TLDs and RFC 920
1984Domain registration requirements are published. The first top-level domains (TLDs) are created: .com, .edu, .gov, .mil, .org and .net, laying the foundations of the hierarchical naming structure we know today.
First .com Domain: symbolics.com
1985On March 15, 1985, Symbolics Inc., a computing company from Cambridge, Massachusetts, registers symbolics.com, making it the first .com domain in history. By the end of 1985, only 6 .com domains were registered. Today there are over 350 million domains registered worldwide.
BIND - The Reference DNS Server
1986Students at the University of California, Berkeley develop BIND (Berkeley Internet Name Domain), the first complete implementation of the DNS protocol. BIND quickly becomes the most widely used DNS software in the world, a position it maintains to this day. It is currently maintained by the Internet Systems Consortium (ISC).
RFC 1034 and 1035 - The Definitive Specification
1987Paul Mockapetris publishes RFC 1034 (Domain Names - Concepts and Facilities) and RFC 1035 (Domain Names - Implementation and Specification), replacing the original RFCs and establishing the definitive DNS specifications. These documents remain the fundamental basis of the current DNS system, more than 35 years later.
InterNIC and the Web Takes Off
1993The National Science Foundation creates InterNIC to manage domain registration, entrusting operations to Network Solutions. With the arrival of the Mosaic browser and Tim Berners-Lee's World Wide Web gaining traction, the number of registered domains begins to grow exponentially. DNS transitions from a technical tool to critical global infrastructure.
NOTIFY, IXFR and the Domain Boom
1995-96RFC 1996 introduces NOTIFY for active synchronization between DNS servers. RFC 1995 enables incremental zone transfers (IXFR), improving DNS replication efficiency. Meanwhile, .com domain registration skyrockets with the Internet boom: going from thousands to millions of domains in just a few years.
Dynamic DNS (DDNS)
1997RFC 2136 introduces the ability to dynamically and automatically update DNS records, without the need to manually edit zone files. This advancement is crucial for networks with changing IP addresses and for DHCP integration.
ICANN Founded
1998The Internet Corporation for Assigned Names and Numbers (ICANN) is founded, a non-profit organization responsible for the global coordination of the Internet's unique identifier systems, including domain names and IP addresses. ICANN takes over functions previously performed by IANA under the U.S. Government, marking a step toward global Internet governance.

Wikimedia Commons / CC BY-SA 4.0
EDNS - Extension Mechanisms
1999RFC 2671 introduces EDNS0 (Extension Mechanisms for DNS), modernizing the protocol to allow larger DNS messages (overcoming the original 512-byte limit) and adding new functionalities. EDNS is essential for DNSSEC and other subsequent protocol improvements.
DNSSEC Deployed in Practice
2005Although DNS Security Extensions (DNSSEC) are defined in RFC 4033-4035, their real-world deployment begins to take shape. DNSSEC allows verifying the authenticity and integrity of DNS responses using cryptographic signatures, protecting against cache poisoning and man-in-the-middle attacks.
Kaminsky Vulnerability - DNS Crisis
2008Security researcher Dan Kaminsky discovers a critical vulnerability in the DNS protocol that allows poisoning the cache of virtually any DNS server in the world. The coordinated disclosure with major software vendors generates one of the largest synchronized security updates in Internet history. This event dramatically accelerates DNSSEC adoption.

Wikimedia Commons / CC BY 2.0
Google Public DNS (8.8.8.8)
2009Google launches its public DNS service with the memorable addresses 8.8.8.8 and 8.8.4.4. It is the first large-scale public DNS service backed by a mega-corporation, offering greater speed and security than most ISP DNS servers. This marks the beginning of the free public DNS era.
Root Zone Signs with DNSSEC
2010On July 15, 2010, the DNS root zone is signed with DNSSEC, a fundamental milestone that enables the cryptographic chain of trust from the root to individual domains. Internationalized domain names (IDN) with non-ASCII characters are also launched.
New gTLDs Program
2012ICANN opens the new generic top-level domain (gTLD) program, allowing companies and organizations to create their own domain extensions. 1,930 applications are received, resulting in hundreds of new TLDs like .app, .blog, .shop, .tech and many more, radically transforming the domain name landscape.
Dyn DDoS Attack - Internet Shakes
2016On October 21, 2016, a massive DDoS attack against DNS provider Dyn, executed by the Mirai botnet composed of IoT devices, makes sites like Twitter, Reddit, Netflix, GitHub and many more inaccessible for hours. The incident demonstrates the criticality of DNS infrastructure and the vulnerability of depending on few providers.
Cloudflare 1.1.1.1 and DNS over HTTPS
2018On April 1, 2018, Cloudflare launches 1.1.1.1, the "world's fastest DNS" according to independent benchmarks. That same year, RFC 8484 standardizes DNS over HTTPS (DoH), allowing DNS queries to be encrypted within normal HTTPS connections. Firefox and Chrome begin implementing DoH, marking a revolution in DNS privacy.
DNS over TLS Consolidates
2019DNS over TLS (DoT, RFC 7858) gains massive adoption. Android 9+ integrates it natively as "Private DNS". Unlike DoH, DoT uses a dedicated port (853), making it easier to manage in corporate networks. Together with DoH, it marks the end of the plaintext DNS era.
DNS over QUIC and DNS4EU
2022RFC 9250 standardizes DNS over QUIC (DoQ), a protocol that combines the advantages of DoH and DoT with lower latency thanks to the QUIC protocol. Meanwhile, the European Union announces DNS4EU, a European sovereign DNS service designed to ensure European citizens' privacy and GDPR compliance.
The Future of DNS
2024+DNS continues evolving with technologies like Oblivious DNS over HTTPS (ODoH) for greater privacy, DNS over HTTP/3, and post-quantum encryption standards. With over 350 million registered domains and trillions of daily DNS queries, the system invented by Paul Mockapetris in 1983 remains the invisible backbone of the Internet.
Ready to improve your DNS?
Choose the best free DNS server for your needs and configure it in minutes.